What is Multi-tenancy? Multi-tenant Architecture in SaaS

Multi-tenancy is an architecture in which a shared application and infrastructure serve multiple independent customers simultaneously, with each customer managed as a distinct tenant. This article presents the concept of multi-tenancy, common data architecture models, implementation challenges, and suggestions for choosing the right approach for SaaS systems.
Key Takeaways
- Concept: Understand that Multi-tenancy is a multi-tenant architecture that helps optimize infrastructure resources while ensuring privacy and logical data separation for each customer.
- Superior Advantages: Grasp the benefits of economies of scale, centralized maintenance, and flexible scalability, enabling SaaS businesses to operate systems efficiently with optimized costs.
- Data Models: Clearly distinguish between three storage architectures - Single Database, Separate Schema, and Shared Schema to choose a solution that balances data isolation and system performance.
- Challenges and Solutions: Identify challenges regarding data isolation, the Noisy Neighbor problem, and backup mechanisms, then equip yourself with handling techniques for stable system operation.
- FAQ: Get answers to questions related to Multi-tenancy architecture.
What is Multi-tenancy?
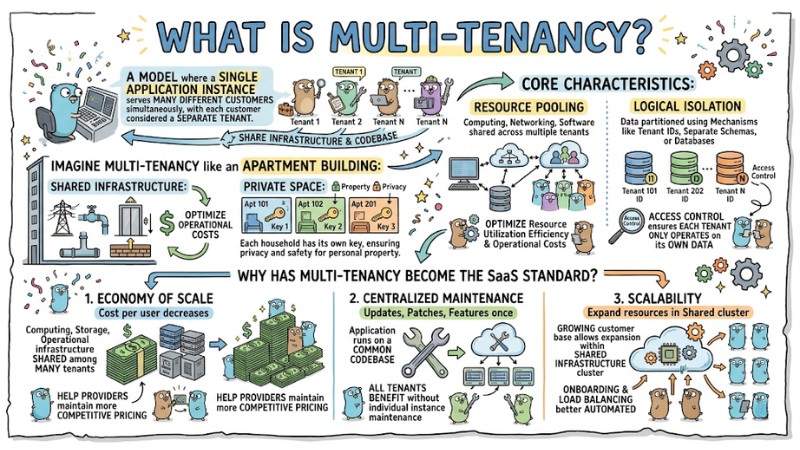
Multi-tenancy (multi-tenant architecture) is a model in which a single instance of an application serves multiple different customers simultaneously, with each customer considered a separate tenant. Tenants share the infrastructure and codebase, but the data, configuration, and access permissions of each tenant are logically separated so they cannot access each other cross-wise.
Imagine Multi-tenancy like an apartment building:
- Shared Infrastructure: All apartments share the same electricity, water, elevator system, and foundation. This helps optimize operational costs.
- Private Space: Each household has its own key, ensuring privacy and safety for personal property.
The core characteristics of this architecture include:
- Resource Pooling: Computing infrastructure, networking, and software are shared across multiple tenants, optimizing resource utilization efficiency and operational costs.
- Logical Isolation: Data and state for each tenant are partitioned using mechanisms like tenant IDs, separate schemas, or separate databases, combined with access control to ensure each tenant only sees and operates on its own data.
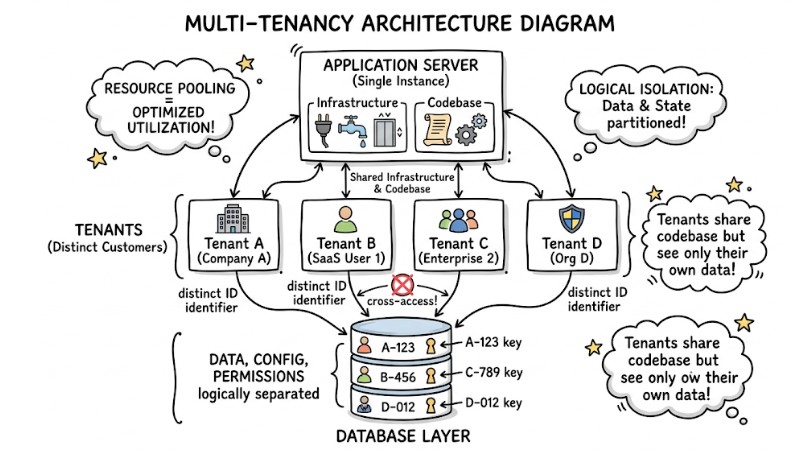
Multi-tenancy architecture with 1 Application Server connecting to multiple Tenants
Why has Multi-tenancy become the standard for SaaS software?
Multi-tenancy has become the default architecture in SaaS because it helps providers optimize operational costs while scaling customers without having to replicate infrastructure for each party. The three main benefits of Multi-tenancy include:
- Economy of Scale: Computing, storage, and operational infrastructure are shared among many tenants, so the cost per user decreases as the number of customers increases, helping providers maintain more competitive pricing.
- Centralized Maintenance: The application runs on a common codebase, so updates, patches, or feature additions only need to be deployed once; all tenants benefit without having to maintain individual instances.
- Scalability: As the customer base grows, providers only need to expand resources within the shared infrastructure cluster instead of reconfiguring multiple independent installations, making new tenant onboarding and load balancing better automated.
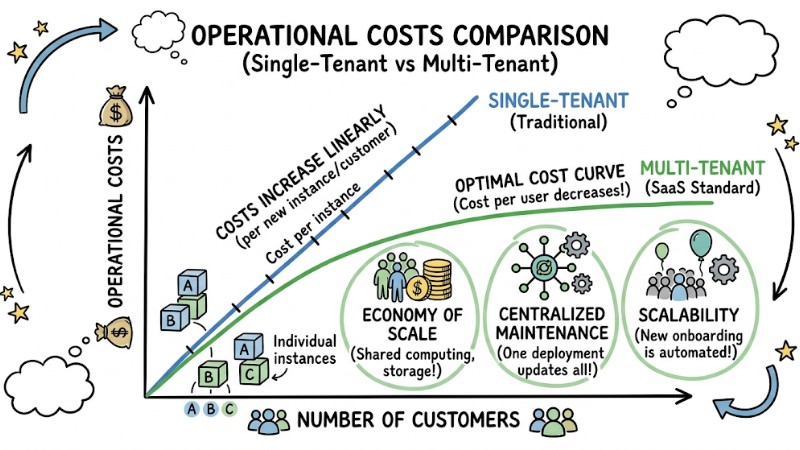
Single-tenant increases linearly with the number of customers, while Multi-tenant maintains an optimal cost curve
Comparing 3 Common Data Architectures in Multi-tenancy
Choosing a storage model is one of the most important decisions when designing a multi-tenant system. The following three models are frequently used in modern SaaS architecture:
- Single Database (One database per tenant): Each customer has an independent physical or logical database, which increases the level of data isolation and supports high compliance requirements, but operational, monitoring, and schema migration costs for multiple databases increase significantly as the number of tenants grows.
- Separate Schema (One schema per tenant): Multiple tenants share the same database, but each tenant has its own schema containing their tables, creating a balance between data isolation and cost while allowing per-tenant customization, though it still requires more complex schema management as tenant counts rise.
- Shared Schema (Shared tables): All tenants share a single set of tables, and each record has a
tenant_idcolumn to distinguish data. This model is simple to implement, saves resources, and makes it easy to run simultaneous migrations, but it requires strict discipline at the application layer to always filter bytenant_idto avoid cross-data leaks.
Example query with tenant_id in a shared schema model:
-- Example: Querying data with Tenant ID
SELECT * FROM orders
WHERE tenant_id = 'KH-001'
AND order_date > '2023-01-01';
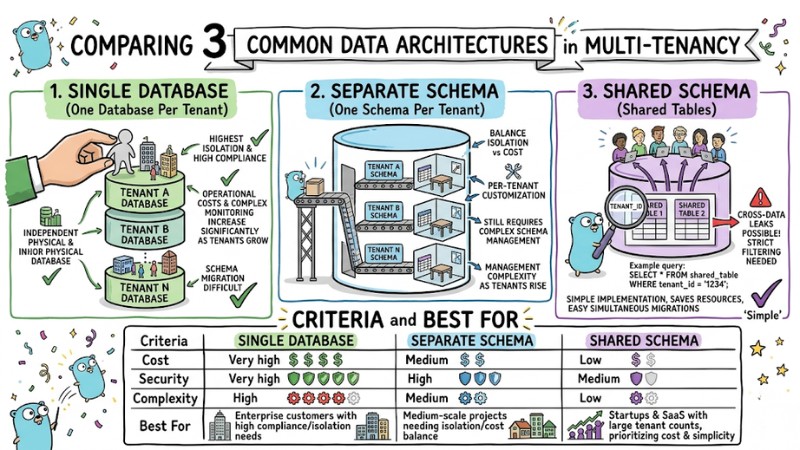
Comparing three common data architectures in multi-tenancy
Table for choosing the suitable Multi-tenancy architecture:
| Criteria | Single Database | Separate Schema | Shared Schema |
|---|---|---|---|
| Cost | Very high | Medium | Low |
| Security | Very high | High | Medium |
| Complexity | High | Medium | Low |
| Best For | Enterprise customers with high compliance/isolation needs | Medium-scale projects needing isolation/cost balance | Startups and SaaS with large tenant counts, prioritizing cost and simplicity |
Pro-tip: Most early-stage SaaS usually choose a shared schema to reduce infrastructure costs and simplify operations, only considering higher isolation models as security requirements or per-tenant customization needs increase.
Challenges in Implementing Multi-tenant Systems
When many customers share a single platform, multi-tenant architecture requires careful handling of data isolation, resource sharing, and backup planning. Here are some common challenges and popular solutions:
- Data Isolation: You must ensure there is no cross-access of data between tenants despite sharing infrastructure. Row-Level Security (RLS) with a
tenant_idcolumn can be applied so the database automatically filters by the current tenant, reducing dependence on application-layer logic. - Noisy Neighbor: A tenant with heavy traffic or queries can degrade performance for other tenants. Implement per-tenant rate limiting, resource quotas, and heavy query monitoring to prevent one customer from monopolizing system capacity.
- Backup/Restore: In a shared schema model, restoring data for a single tenant is more complex than restoring the entire database. Therefore, many systems add logical backup mechanisms or tenant-based data exports to enable recovery or migration of individual customers when needed.
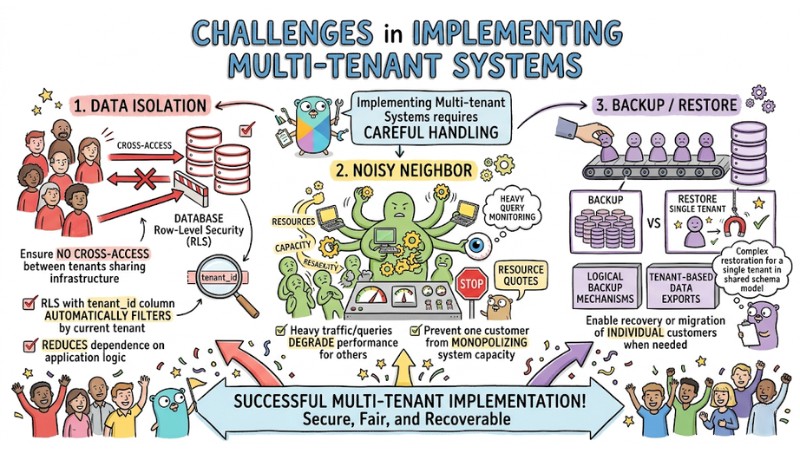
Some challenges when implementing a multi-tenant system
FAQ
How do I ensure customer data is not mixed?
You should use tenant_id in every query, apply access control mechanisms, and utilize Row Level Security so the database automatically filters data according to the current tenant.
Is it possible to switch from Shared Schema to another model?
Yes, but it requires data migration, code updates, and downtime. Therefore, it is usually only performed when scale and security requirements change significantly; it is best to carefully consider the model during the initial design phase.
Does Multi-tenancy affect application load speed?
If optimized with good indexing on the tenant_id column and main query columns, and with proper resource allocation for each tenant, multi-tenancy still achieves high performance with no significant difference from a single-tenant model.
Read more:
- What is a Multi-Agent System? Overview and Top 7 Practical Use Cases
- 15 Important Multi-Agent Metrics for Evaluating AI Agent Systems
- What is Multi-Agent Workflow? Architecture, Models and Applications
Multi-tenancy architecture helps SaaS systems optimize costs, simplify operations, and scale customer numbers while maintaining an appropriate level of data isolation for each architectural model. When designing, you need to choose a storage model and tenant isolation strategy from the start, combining techniques like tenant_id, access control, and tenant-based backups to balance performance, security, and scalability.