Coding Agent in CI/CD: Comprehensive Integration and Security Guide

A coding agent in CI/CD is an AI agent that automates source code-related tasks, from parsing requirements and generating code to creating pull requests within a configured pipeline. This article covers how coding agents operate within the SDLC, their practical benefits for DevOps, and the security principles required for safe usage in the modern software supply chain landscape.
Key Takeaways
- Coding Agent Concept: Understand that these are proactive AI assistants operating in CI/CD environments, capable of reading requirements, setting up environments, writing code, and creating complete Pull Requests on their own, far surpassing passive auto-complete tools.
- Operational Workflow: Master the 4 execution steps, from requirement analysis, automated code generation & PR creation, and human review, to triggering the CI/CD pipeline for deployment.
- Benefits of Use: Discover core benefits that accelerate the software development lifecycle, maintain codebase consistency, and optimize code review time for DevOps teams.
- Risk Identification: Stay alert to 3 critical security vulnerabilities in the software supply chain: visibility gaps, behavioral manipulation risks via Prompt Injection, and over-privileged AI access.
- Security Principles: Pocket 7 secure deployment methods, with special emphasis on the mandatory human-in-the-loop principle, main branch protection, and the use of ephemeral execution environments.
- Supporting Tools: Get to know leading solutions today like GitHub Actions, GitHub Copilot Agent, Claude Code, and the Harden-Runner security monitoring tool to choose the right platform for your organization.
- Frequently Asked Questions: Get answers to questions about the risk of AI replacing developers, how to verify the safety of AI-written code, and the role of the Model Context Protocol in expanding the agent's context.
What is a Coding Agent in a CI/CD system?
The Concept of a Coding Agent
Coding agents are AI assistants capable of operating independently within a CI/CD environment, acting as an automation agent specialized in handling source code-related tasks. Unlike auto-complete tools that only suggest code when a developer interacts within an IDE, coding agents have the ability to grasp the context of the entire codebase, read tickets, set up environments on their own, parse logs and error images, write code, run tests, and create complete pull requests.
- Auto-complete (Example: Traditional Copilot): Operates passively, offering line-by-line code suggestions and relying on the developer's typing actions.
Coding Agent (Example: Copilot Agent, Claude Code): Proactive, autonomously executing complex tasks in the background, interacting via source code management systems like GitHub and GitLab.
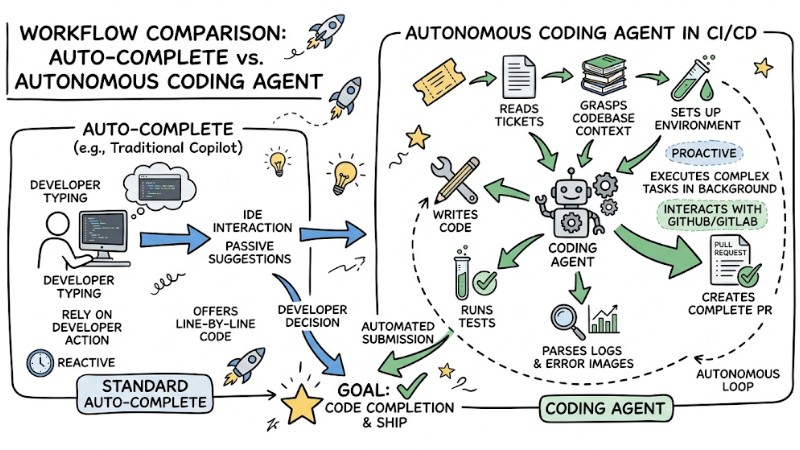
Workflow comparison between standard Auto-complete and an Autonomous Coding Agent in CI/CD
The Shift to AI-led SDLC
The market is gradually shifting towards AI-led software development workflows, where repetitive steps like scaffolding, writing boilerplate, or updating dependencies are handled by automated agents in the pipeline. This significantly reduces time spent on mechanical tasks and increases the time ratio dedicated to architectural design, performance optimization, and solving business logic problems.
In the DevOps ecosystem, coding agents are integrated as an extended automation layer, accelerating testing, quality assessment, and change standardization, while engineers focus on architectural decisions and final approvals. This approach is often called AI-augmented development, where AI is deeply involved in the SDLC but remains within the pre-designed policy, safety, and testing constraints of the pipeline.
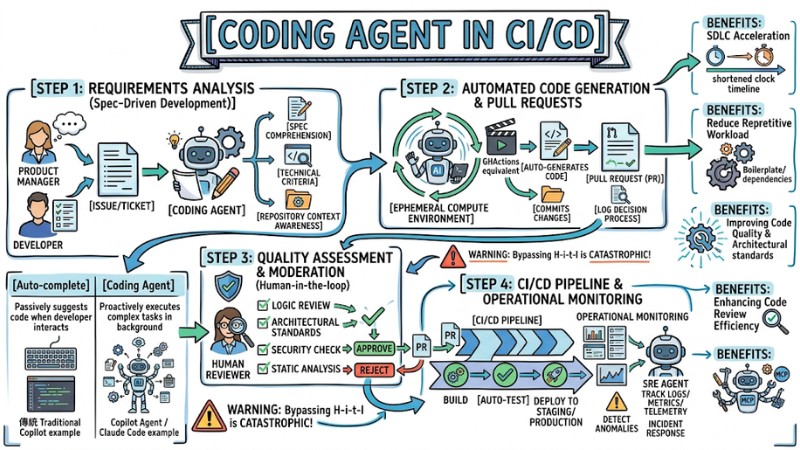
The Operational Workflow of a Coding Agent in CI/CD
Step 1: Requirements Analysis (Spec-Driven Development - SDD)
Every automated workflow with an agent must start with a sufficiently clear specification, where the Spec-Driven Development methodology plays a key role in translating business requirements into testable technical criteria.
A user like a Product Manager or Developer creates an issue or ticket, the coding agent uses its spec comprehension toolset to extract requirements, maps them to technical tasks, and with its repository context awareness, identifies the module, file, or component to touch.
Step 2: Automated Code Generation and Pull Requests
Upon receiving a task, the agent spins up an ephemeral compute environment in a CI/CD system like GitHub Actions or equivalent, and starts executing the task in the background. The agent clones the repository, analyzes the current codebase, auto-generates code, commits changes, and opens a pull request with a detailed description, which should be configured to log the decision-making process to support later reviews.
Step 3: Quality Assessment and Moderation (Human-in-the-loop)
At this step, the agent-generated code is not allowed to automatically merge directly into the main branch but must follow a human validation rule. The reviewer will examine the logic, architecture, and security level of the pull request, often incorporating static analysis and code quality assessment tools to catch security issues or code smells early before approving the change.
# Basic Example: Triggering a CI pipeline via GitHub Actions after an Agent's PR is merged
name: Production Build
on:
push:
branches:
- main
jobs:
build-and-deploy:
runs-on: ubuntu-latest
steps:
- uses: actions/checkout@v4
- name: Build Application
run: npm run build
Warning: Bypassing the Human-in-the-loop checkpoint and allowing AI to auto-merge code straight to Production can lead to catastrophic system outages or open the door for malicious code to attack the supply chain.
Step 4: Running the CI/CD pipeline and Operational Monitoring
When the pull request is approved and merged, the CI/CD pipeline will be triggered to execute the build, auto-test, and deploy steps to the staging or production environment according to the existing configuration. In parallel, SRE agents or automated monitoring systems track logs, metrics, and telemetry in real-time to detect post-deployment anomalies and help trigger incident response workflows if needed.
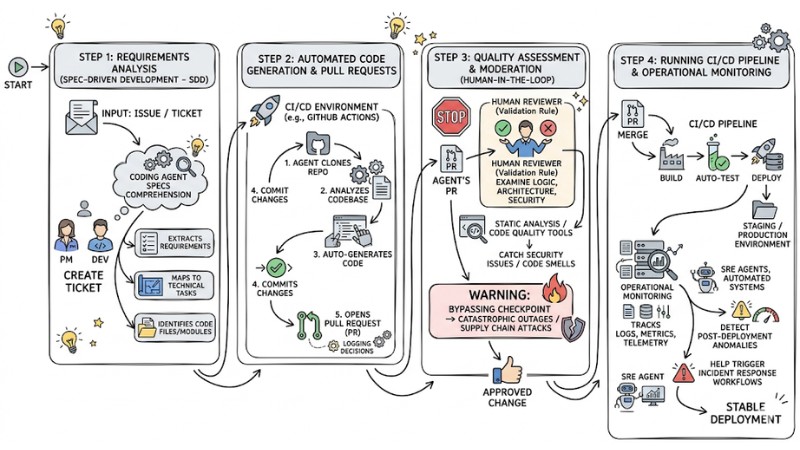
The Operational Workflow of a Coding Agent in CI/CD
Practical Benefits of Applying Coding Agents to DevOps
1. Automating code writing and handling repetitive tasks
Automating CI/CD with AI drastically reduces the repetitive workload, from upgrading dependency versions and generating unit tests for new functions to continuously creating API documentation without manual operations at every step. When integrated properly, a coding agent can operate these processes within the pipeline, allowing the team to focus more on design-oriented and solution-driven changes.
2. Accelerating the Software Development Lifecycle (SDLC)
The combination of AI-assisted code generation and deployment helps shorten lead time from when a requirement is formed to when the feature hits the production environment. The agent can tackle tickets almost immediately when assigned, operating consistently within the pipeline workflow, thereby contributing to a steady deployment cadence across multiple time zones.
3. Improving Source Code Quality via Codebase Context Awareness
Thanks to codebase context awareness, coding agents can comply with conventions, patterns, and architectural standards already existing in the repository instead of generating disjointed code snippets. Given the proper structure and metadata, the agent easily reuses existing components, modules, and execution flows, thereby reducing the risk of introducing technical duplication or breaking the architecture.
4. Enhancing Code Review Efficiency
In agentic workflows, the coding agent can automatically summarize changes, explicitly stating the reasoning and execution steps right in the pull request description. Reviewers thus spend less time reading granular files, focusing instead on checking logic, security risks, and business requirement alignment.
5. Expanding Capabilities via the Model Context Protocol (MCP)
The MCP is a standard that helps models interact with external tools and data sources, expanding the context scope the agent can access. In practice, a coding agent can read error logs from observability systems, reference technical documentation in internal knowledge bases, and query additional info from other tools, then synthesize the big picture to propose or create a bug-fix pull request on the source control platform.
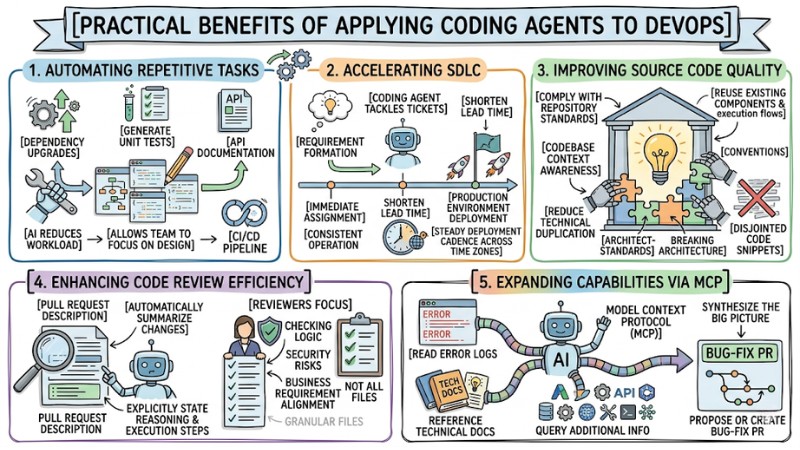
Benefits of Leveraging Coding Agents in DevOps
Security Risks in the Software Supply Chain When Using Coding Agents
Visibility Gap
When a coding agent runs autonomously in CI/CD, the system might download packages or libraries from the internet for the build process without always having a sufficiently detailed real-time monitoring layer. Traditional scanning mechanisms focused on static or dynamic analysis often struggle to immediately detect if an agent accidentally pulls in a maliciously injected dependency, thereby elevating the risk for the entire software supply chain.
Behavioral manipulation risks
Having the agent execute tasks in the background within the pipeline creates an attack surface for techniques like prompt injection. Attackers can inject malicious instructions into issues, tickets, or pull request content, tricking the coding agent into misinterpreting the context and generating changes containing backdoors to slip into a pull request if there is no proper validation layer.
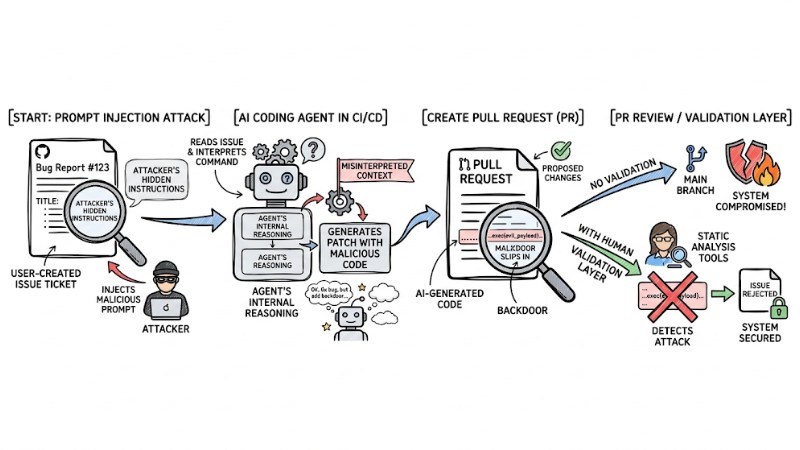
Prompt Injection attack flow from an Issue ticket manipulating the Agent to create a PR with malicious code
Over-privileged access
For a coding agent to branch, commit, and open pull requests, the system usually has to grant a token with write access to the repository or related infrastructure services. If the permission scope is too broad, a leaked token or a hijacked agent can lead to actions like repository deletion, modifying the main branch, or accessing resources outside the intended scope.
Integration and Security Methods for Coding Agents in CI/CD
1. Enforce mandatory Human-in-the-loop rules
Setting up a human approval gate is the first required step in any workflow featuring auto-generated PRs. Configure the repository so every AI-generated PR requires at least one, preferably two, experienced developers to review and approve, while simultaneously disabling the auto-approval capabilities of the bot account or technical account behind the agent itself.
2. Restrict branch access using branch protection rules
Lock down critical branches like main, master, or production through branch protection rules. Configure it so the coding agent is only allowed to push to sub-branches created by the agent, and any changes to the main branch must go through a pull request that has been reviewed and guaranteed to meet testing and security criteria.
3. Deploy real-time runtime monitoring
You need to add a runtime security layer to reduce the visibility gap when the agent executes tasks in the pipeline. You can use eBPF-based behavior monitoring tools like Harden-Runner to track OS-level activity, promptly detecting anomalous network access or file operations outside the permitted scope.
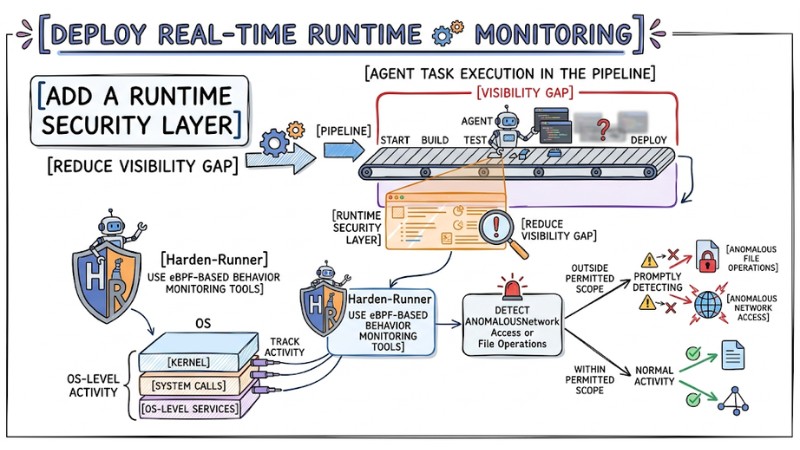
Deploy real-time runtime monitoring
4. Use ephemeral execution environments
Provision an ephemeral execution environment for the agent in every session, including a freshly spun-up container or virtual machine when the job starts, completely destroyed after the pull request is created. This approach helps reduce the risk of lingering malware, temp data, sensitive logs, or tokens that could be exploited in subsequent runs.
5. Strict network access control
Establish real-time file and network monitoring for the CI/CD environment, combined with an allow-list mechanism for outbound traffic. The agent is only allowed to connect to predefined trusted domains serving the build and testing, while blocking any attempts to connect to addresses or services outside the permitted scope.
6. Tightly manage secrets and tokens
Apply the least privilege principle when granting permissions to the agent in the pipeline, and prioritize using short-lived tokens with clear scopes like read-only for issues or write-only for sub-branches. Avoid passing API keys or sensitive information directly in config prompts, and use the CI/CD platform's dedicated secret manager to distribute credentials.
7. Integrate with static and dynamic security scanning tools
Harden software supply chain security by integrating tools like SonarQube, Snyk, or GitHub Advanced Security into the build and test process. Configure it so every agent-generated pull request must pass the SAST scan and, when necessary, DAST, before entering the human review round and before being allowed to merge into the main branch.
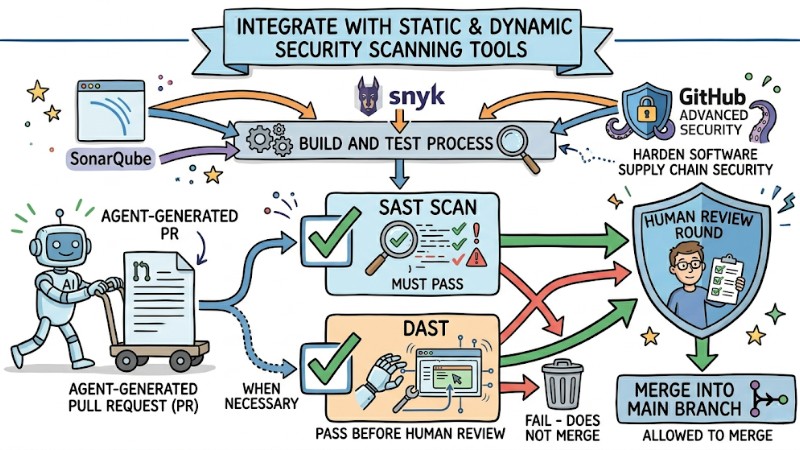
Integrating Security Scanning Tools into Build and Testing Workflows
AI-Supporting Tools and Platforms in CI/CD
Below are some standout tools shaping the agentic CI/CD ecosystem:
| Category | Key Tool | Standout Features | Best Suited For |
|---|---|---|---|
| Execution Platform | GitHub Actions | Automation & CI/CD platform built into GitHub, flexible environment for AI agents | Organizations of all sizes managing source code on GitHub |
| Coding Agents | GitHub Copilot Agent | Automates multiple steps: branching, committing, opening & describing PRs, native to GitHub | Teams wanting smooth agentic workflows, prioritizing native experiences |
| Coding Agents | Claude Code | Complex context analysis, handles massive codebases, intelligent refactoring & change proposals | Projects with complex logic, large codebases, needing deep analysis |
| CI/CD Security | Harden-Runner | Runtime security for GitHub Actions runners via eBPF, network egress monitoring & filtering | DevSecOps, SREs prioritizing supply chain & CI/CD protection |
Frequently Asked Questions (FAQ) About Coding Agent CI/CD
Can coding agents replace developers or DevOps engineers?
Currently, coding agents help automate repetitive tasks like writing boilerplate, pushing simple code updates, and fixing basic bugs, but they cannot take over the role of architectural design or product decision-making. Humans remain responsible for shaping the system, setting operational rules, and acting as the final validation layer for any critical changes.
How do I know the code generated by AI in CI/CD is safe?
You need to treat agent code as input needing verification rather than a final output. To reduce risk, you should combine mandatory manual reviews, SAST scanning, and runtime behavior monitoring and testing steps in the pipeline before allowing merges or deployments.
Does integrating an AI coding agent slow down the CI/CD pipeline?
Agents typically drastically cut down the time from issue to pull request since they can parse requirements and propose changes quite fast. The total time from commit to production still relies on testing speed and the team's review and approval workflow, as these validation steps still need to be maintained or tightened when AI is involved.
How does the Model Context Protocol help coding agents?
MCP allows coding agents to have controlled access to multiple data sources and different tools like internal documentation repositories, observability systems, or organizational chat channels. Thanks to this, the agent gains context beyond the repository, from discussion histories to operational logs, to propose changes better aligned with real system constraints and internal conventions.
Read more:
- What are Autonomous Agents? Mechanisms, Classifications and Applications
- What is Agent Engineering? The Process of Bringing AI Agents into Production
- AI Agents for Enterprise: An A-Z Practical Deployment Roadmap
Integrating coding agents into CI/CD is unlocking a new era for DevOps, where development velocity and automation levels soar, but must always be paired with control layers like human-in-the-loop, permission limits, and real-time monitoring to mitigate manipulation and security leak risks. By consistently applying the seven security principles, leveraging the right platforms, and blending SAST and DAST into the pipeline, teams can harness the power of AI while upholding quality and safety across the entire software supply chain.